Global Cyberattack on Energy Sector Stokes Deep Fears | Cybersecurity
By John P. Mello Jr.
Sep 7, 2017 11:11 AM PT
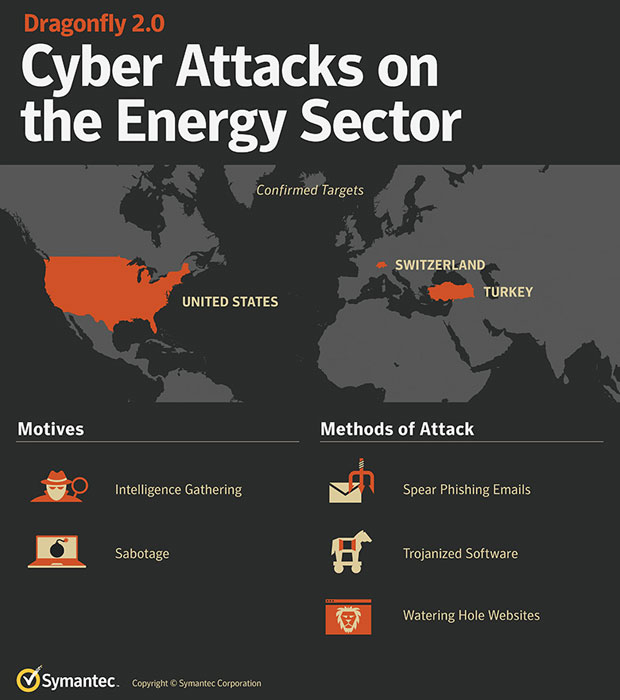
The hacker group known as “Dragonfly” is behind sophisticated wave of recent cyberattacks on the energy sectors of Europe and North America, Symantec reported Wednesday.
The attacks could provide the group with the means to severely disrupt energy operations on both continents.
Dragonfly launched a simililar campaign from 2011 to 2014, but it entered a quiet period in 2014 after Symantec and others exposed its activities.
The current campaign began in December 2015, Symantec noted.
The firm found strong indications of Dragonfly activity in the United States, Turkey and Switzerland, and traces of activity in places outside those areas.
Dragonfly’s Most Recent Activities
The attackers have employed a number of methods to infect systems, including malicious emails, watering hole attacks and Trojanized software.
Gravity of Situation
“Breaching of multiple energy sector organizations is extremely concerning,” said Eric Chien, technical director of Symantec’s Security Response and Technology Division.
“The U.S. power grid is large and complex, and there isn’t a single switch that turns off the electricity for the entire United States,” he told TechNewsWorld.
“However, access to operational systems within multiple energy sector organizations could lead to significant disruption.”
Although the impact of the attacks so far has been minimal, that doesn’t mitigate the need for concern.
“The future is what’s at play here,” said Dana Tamir, vice president of market strategy at
Indegy.
“This might be an attempt to gain information about these systems in preparation of future attacks,” she told TechNewsWorld. “The fact that nothing’s happened right now doesn’t mean that nothing will happen in the near future.”
Unclear Motives
Security researchers have yet to determine the motives behind the energy sector attacks.
“We are not seeing any motivation in regards to monetary, extortion or economic espionage,” Symantec’s Chien said.
“We do not know the ultimate motivation of the attacker, but clearly disruption and sabotage are candidates with access to such systems,” he added.
The characteristics of the attacks point to a class of perpetrator, observed Indegy’s Tamir.
“The sophistication of the attack, the targets of the attack, the gathering of information indicates there’s a bigger play here that’s more typical of a nation-state than a criminal organization,” she said.
Tools of the Trade
While the campaign itself is sophisticated, the tools and methods used by the attackers to penetrate the
SCADA industrial control systems are not.
“What’s interesting here is the relatively unsophisticated methods the hacking group has used,” said Leigh-Anne Galloway, cybersecurity resilience lead for Positive Technologies.
“Usually with SCADA, the tactic of choice is to exploit zero-day vulnerabilities,” she told TechNewsWorld. “In this case, though, they’ve chosen to go for the older but most-effective methods of phishing and watering holes to get in.”
The Dragonfly hackers use their tools to collect credentials and perform reconnaissance on the systems they’re attacking, noted Indegy’s Tamir.
“Once they get that information and penetrate the systems themselves, manipulating the systems does not require any special tools,” she said. “The systems are quite easy to manipulate once you’re inside them.”
“We are seeing the attackers increasingly ‘live off the land’ by using default system administration tools in order to penetrate systems, as well as reusing and modifying existing off-the-shelf malicious software,” added Symantec’s Chien.
Countering the Attacks
Since discovering the latest activity, Symantec has briefed more than 100 energy sector and government organizations in the United States and Europe and made recommendations to them about coping with the attacks.
“The power grid penetration incidents are terrifying,” said Varun Badhwar, CEO of
RedLock.
“They really hit home the importance of having a solid cybersecurity strategy in place for organizations of all types,” he told TechNewsWorld.
Attacks on industrial control systems have been increasing in recent times, according to a new
report from IBM Security.
There were 2,788 attacks in 2016, up from 640 attacks in 2013, for instance. That trend appears to be continuing this year. Through July, IBM already had reported 2,522 attacks.
“There’s growing awareness,” Indegy’s Tamir observed, “but the energy sector is moving too slow to address these threats.”
![]()

 John P. Mello Jr. has been an ECT News Network reporter
John P. Mello Jr. has been an ECT News Network reporter